What’s Trending in Manufacturing
What’s Trending in Manufacturing
By John Killam, President, MassMEP
In 2017, the DoD issued a mandate that by December 31, 2017, all DoD contractors (including small businesses) must meet minimum cybersecurity requirements or risk losing DoD business.Manufacturing companies that produce products for contractors of the Department of Defense (DoD) face new challenges when it comes to complying with cybersecurity regulations. Perhaps the first hurdle is that many don’t even know they are required to do this! Few are aware of the DOD’s cybersecurity regulations, never mind how to comply. But don’t fret, the MassMEP can help navigate these uncharted waters.
- Ensure that any unclassified DoD information kept on a contractor’s/vendor’s internal data system is safeguarded from cyber attacks, and
- Any consequences associated with a breach are assessed and minimized via the cyber incident reporting and damage assessment processes.
How Did This Come About?
The Joint Task Force Transformation Initiative was launched in April 2009 by the DoD and Office of the Director of National Intelligence (DNI). The goal of the Initiative was to create cybersecurity standards consistent across different federal agencies. As this was developing, Congress added additional requirements to the National Defense Authorization Act (NDAA).
In 2015, The National Institute of Standards and Technology (NIST) developed cybersecurity standards (Special Publication 800-171 “Protecting Controlled Unclassified Information in Non-federal Information Systems and Organizations”) that the DoD implemented in their policies and the Defense Federal Acquisition Regulation Supplement (DFARS). The publication was revised in December 2016.
We’re a small manufacturing company. Do we really need to worry about cybersecurity? The short answer is, Yes!
Most small manufacturers don’t consider the impact of a cybersecurity breach. But today, as hackers become more adept at accessing systems, cyber attacks can come in many forms: phishing, web attacks, spam, identity theft, and ransomware.
Even small business can be hacked. In fact, the majority (70%) of reported breaches affected small businesses with fewer than 100 employees. A sustainable plan is vital for a small business’ survival – one cyber attack can devastate a business.
What Does this Mean for My Small Business?
As a small business contracting with the DoD, you are required to adhere to two basic cybersecurity standards:
1. Provide adequate security to protect defense information kept on internal data systems. The standards include:
- Access Control Media
- Awareness & Training
- Audit & Accountability Configuration Management
- Identification & Authentication Incident Response Maintenance
- Media Protection
- Personnel Security
- Physical Protection
- Risk Assessment
- Security Assessment
- System & Communications Protection System & Information Integrity
2. Immediately report any cyber breaches/issues and cooperate with DoD to respond to these.
MassMEP has established an integrated approach with multiple solutions to work with Massachusetts manufacturing companies to determine the best solution for them.
What Do I Do if a Breach is Discovered?
1. Don’t panic. Cybersecurity occurs in a dynamic environment. Hackers are constantly coming up with new ways to attack information systems and DoD is constantly responding to these threats. So, even if a contractor does everything right and institutes the strongest checks and controls, it is possible that someone will come up with a new way to penetrate these measures. DoD does not penalize contractors acting in good faith. The key is to work in partnership with DoD so that new strategies can be developed to stay one step ahead of the hackers.
2. Contact DoD immediately – in fact, a breach must be reported to the DoD within 72 hours of discovery. An online form is available for reporting the breach.
3. Contact MassMEP to determine how to best determine next steps.
How do I meet the SP 800-171 Requirements?
Meeting the SP 800-171 is an ongoing process that involves continuous assessment, monitoring, and improvement. Periodically assess the security controls in your company’s systems to determine if the controls are effective in their application. Develop and implement plans of actiondesigned to correct deficiencies and reduce or eliminate vulnerabilities in systems. Monitor security controls on an ongoing basis to ensure the continued effectiveness of the controls. Develop, document, and periodically update system security plans that describe system boundaries, system environments of operation, how security requirements are implemented, and the relationships with or connections to other systems.
Although these requirements may initially seem overwhelming, small businesses can use this framework to divide the project into small, manageable chunks and work toward attaining compliance.
What is a System Security Plan?
A System Security Plan is a document that describes how a small manufacturer meets the security requirements for a system or how a small manufacturer plans to meet the requirements. The system security plan describes the system boundary, the environment in which the system operates, how the security requirements are implemented, and the relationships with or connections to other systems
How Can I Protect My Company?
Cybersecurity is vital to the health of your business. Ensuring your data is safe protects the integrity and confidentiality of your information and provides numerous advantages. A cybersecurity program can help your business:
- Avoid potential losses
- Ensure employee and customer privacy by protecting confidential information
- Protect valuable business data
- Lessen vulnerability for an attack
It’s important that manufacturers understand and manage the risk and establish a cybersecurity protocol to protect your most critical assets. Based on information provided by the National Institute of Standards and Technology (NIST), MassMEP recommends these steps to help reduce your risk of a cyber attack.
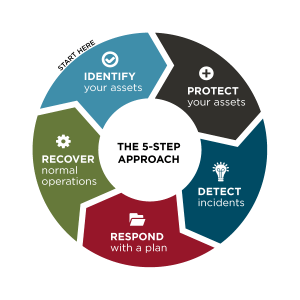
Five Steps to Reduce Cyber Risks
MassMEP has established a structured approach that focuses on the five major steps to reduce cyber risks through a comprehensive set of options and solutions. These simple, low-cost steps are based on the official NIST guidance from the Cybersecurity Framework and have been tailored to meet the needs of small businesses.
- IDENTIFY – Know who has access to your information and maintain control of that access. Ensure risk reduction by conducting background checks on anyone with access. Require each employee to have an individual user account. Create policies and procedures for cybersecurity and ensure your employees are aware of them and understand protocol.
- PROTECT – Limit the number of people who have access to data, safeguard your data by installing surge protectors and Uninterruptible Power Supplies (UPS), ensure you are patching operating systems and applications on a routine basis, install software and hardware firewalls on your networks, secure wireless access points, create web and email filters, utilize encryption software to protect sensitive information, properly and securely dispose of old computers/media, and ensure your employees understand the risks and are trained appropriately.
- DETECT – Be proactive by installing and updating anti-virus controls/software (anti-virus, anti-spyware, anti-malware), develop logs, and monitor usage.
- RESPOND – Be ready to respond and generate a plan for security breaches and disasters to ensure you are able to respond in the most timely manner.
- RECOVER – Install automatic backup software and ensure you are regularly backing up information, make full backups of business data and confidential information, invest in cyber insurance to protect your assets should a breach occur, and continually access and make necessary improvements to cybersecurity processes and procedures.
Additional resources are available at NIST’s web site and a FAQ from the DoD.
Still have questions? Contact MassMEP today to get the help you need to ensure your business meets these new regulations.